Login policy
On this page
Introduction
As data protection is always a high priority, Service Desk administrators can configure the following login policies to further increase data protection while balancing the efficiency and safety requirements desired for your users.
Navigation
| ITSM customers | ESM customers |
|---|---|
| Setup > Account > Login Policy | Organization > Setup > Account > Login Policy |
Policies
Policies include:
- Multi-factor authentication. Select between mobile phone, email, or Google Authenticator (available for all Service Desk accounts).
- Password policy. Customize your password policies to the desired security settings, such as minimum password length, password complexity requirements, length of time before password must be changed, and maximum number of invalid login attempts.
- Session timeout definition. Select between interval-based (frequency of logins required) or inactivity-based (re-login required if user has been inactive for a specified period of time).
- Session timeout definition for mobile application. Toggle to On to require users to re-log in to the mobile application after 12 hours from their last activity.
After an administrator activates the MFA process, your users are prompted at their next login to set up their MFA method of authentication:
- Mobile phone
- Google Authentication
Single sign-on and MFA
If your organization is already using Single sign-on and provisioning (SSO) as your authentication process, you can integrate the SSO feature with Service Desk. SSO vendors usually offer built-in MFA support, so SSO will supercede MFA authentication.
Additional use of MFA would be for external users. Even if your internal team identifies upon login via SSO, external users such as outside contractors can safely log in to Service Desk via MFA without an SSO account.
For more information about single sign-on, see Single sign-on and provisioning
Login Policy settings for ITSM customer vs. ESM customers
Configuration of login policy settings is different for ITSM customers vs. ESM customers.
ITSM customers
Multi-Factor Authentication (MFA) for ITSM customers
To activate multi-factor authentication for some or all of your users:
- Navigate to Setup > Account > Login Policy, and then toggle the pill bar to On.
- Apply to all users or specific roles. If you select Specific roles, click in the Specify roles field to define which roles from the dropdown menu.
 If you select Specific Roles but fail to specify which roles, multi-factor authentication will not be activated.
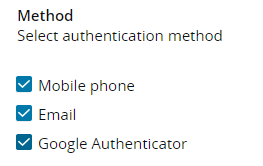
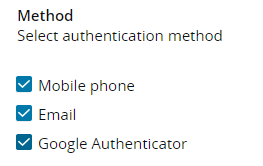
If you select Specific Roles but fail to specify which roles, multi-factor authentication will not be activated. - Under Method, select the method(s) of authentication. You can select one, two, or all three options listed.
See additional information related to multi-factor authentication in Reset MFA setup for a specific user and MFA user experience.
Password Policy settings for ITSM customers
Service Desk offers a number of customization options that allow you to modify your password policies to achieve the desired security settings for both your requesters and service agent users.
Using the two tabs (Requester and Non-Requester) set the following for the selected user role.
- Minimum password length
- Password complexity requirements
- Mixed capitalization
- Mixed capitalization and numbers
- Mixed capitalization, numbers, and special characters
- Password expiration
- Maximum invalid login attempts
Session timeout definition for ITSM customers
Customization options allow you to modify your session policies to require requesters and service agent users to re-log in after set time parameters. Select one of the options to set the time period for your desired security setting, and then select a time frame for that option.
- Interval based
- Inactivity based
ESM customers
Multi-Factor Authentication (MFA) for ESM customers
To activate multi-factor authentication:
- Navigate to Organization > Account > Login Policy, and then toggle the pill bar to On.
- Under Method, select the method(s) of authentication. You can select one, two, or all three options listed.
See additional information related to multi-factor authentication in Reset MFA setup for a specific user and MFA user experience.
Password Policy settings for ESM customers
ESM password settings are set at the Organization level. Both requesters and non-requesters have the same password requirements. Options are:
- Minimum password length
- Mixed capitalization
- Mixed capitalization and numbers
- Mixed capitalization, numbers, and special characters
- Password expiration
- Minimum invalid login attempts
Session timeout definition for ESM customers
Customization options allow you to modify your session policies to require requesters and service agent users to re-log in after set time parameters. Select one of the options to set the time period for your desired security setting, and then select a time frame for that option.
- Interval based
- Inactivity based
Reset MFA setup for a specific user
If at any time a user is unable to complete the login authentication process due to a change in phone number or an unexpected error, an administrator can reset the MFA setup via the button in the User index.

-
Navigate to Users & Groups > Users.
-
From the Users index page, click the link to the user's name to open the record.
-
Click Actions and select Reset multi-factor auth. setup.

MFA user experience
When the user first tries to log in after MFA is activated by an administrator, the user is prompted to authenticate on the user desktop and any mobile devices using Service Desk.
If the authentication method is mobile phone:
-
The user is informed of the new authentication step and is asked to enter a mobile number.

-
A code is sent to the mobile number provided. The user must enter the code at the verification prompt.
The code is only valid for 30 minutes, after which a new code is required.
If the authentication method is Google Authenticator:
-
The user can scan the QR code and enter the verification code provided.

-
The user will be prompted to provide a verification method.

-
After initial setup, the user will always receive a prompt to select which method to receive a verification code.
When a user updates their mobile number on the User profile page, and MFA is active, they need to click Verify to authenticate the phone number via MFA.
