Configure user defined groups
User-defined groups allow you to create groups of values relevant to your IT environment, such as user and computer names, sensitive file locations, trusted IP addresses, and so on. Similar to other groups, user defined groups contain information that can be used in rules and filters.
This section describes how to add and edit values in user-defined groups. You can also create rules that auto-populate user-defined groups with values.
If Active Directory is available, use directory service groups to add user and computer accounts to rules and filters. A user-defined group cannot be synchronized with Active Directory, but a directory service group can synchronize with Active Directory every five minutes. See Configure Directory Service Groups in SEM for details.
How rules and filters use user-defined groups
Below are a few example rules that depend on user-defined groups:
- A rule that stops SEM from blocking accounts in a user-defined group of trusted administrator accounts.
- A second rule that sends out an alert when an account in the same user-defined group of trusted admin accounts logs in or makes changes.
- A rule that checks a user-defined group containing trusted IP addresses to see if it should block a certain IP address.
Rules and filters typically incorporate user-defined groups in slightly different ways:
- In a rule, user-defined groups are typically used like a white list or black list that tell SEM which events it should include or ignore.
- In a filter, user-defined groups limit the scope of the filter to items that belong to the group.
Rules that use user-defined groups include:
- Authentication - Unknown User
- Critical Account Logon Failures
- Detach Unauthorized USB Devices
- File Audit - Delete Sensitive Files
- Non-Admin Server Logon
- Vendor - Unauthorized Server Logon
Filters that use user-defined groups include:
-
Admin Account Authentication
-
Domain Controllers (all)
The Domain Controllers (all) filter uses a connector profile in the constant position by default. You can replace the profile with a user-defined group or a directory service group if the tool profile is not sufficient for your environment. For additional information about connector profiles, see Create connector profiles to manage and monitor SEM Agents.
Create or edit a user-defined group
You can create as many user-defined groups as you need to support your rules and filters.
You can only add a group to one SEM manager at a time. To copy a group for use with another SEM manager, export the group and then import it into the other manager's Groups grid.
- Log in to the SEM Console.
- On the SEM Console, click Configure > User defined groups.
- On the toolbar, click Create User-defined group.
The Create User-defined group window is displayed.
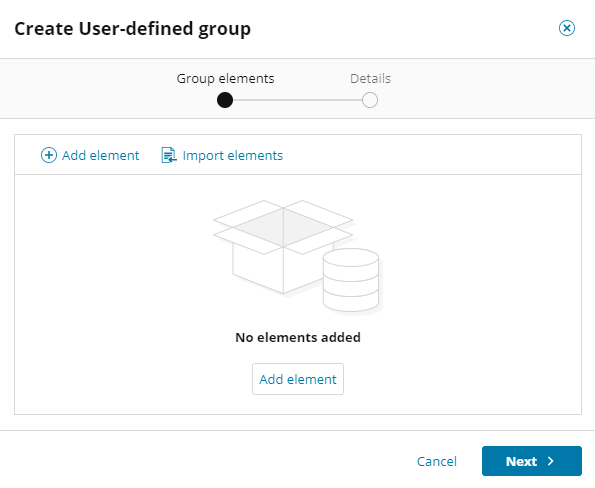
- Click Add element.
-
Complete the fields in the window.

-
In the Name field, enter a nickname for the element. This name is for reference only.
- In the Value field, enter a value to define the element. You can use wildcard characters, such as asterisks (*), to abbreviate these entries.
- In the description field, enter a description (optional), and then click Add.
In the elements list, you can search for a specific element, and select an element to edit the values or delete it. You can also export the elements to a CSV file to import into other user-defined groups.
-
-
Continue to add elements as needed, and then click Next.

-
Add your group name and description (optional), and then click Create.

The new group is displayed in the user-defined groups list. You can use the group when you configure your rules and filters.

Edit a user-defined group
-
Select a group in the list.
-
On the toolbar, click Edit.
-
In the Group elements window, you can filter the groups by the modifier and the time last modified.
-
Make any additional changes, and then click Next.
-
Follow the instructions in the window to finish editing the group.
Customize the blank and sample user-defined groups included with SEM
SolarWinds recommends customizing the following blank and sample user-defined groups for your environment:
- Admin accounts
- Admin groups
- Approved DNS servers
- Authorized USB devices
- Authorized VPN users
- Sensitive files
- Service accounts
- Suspicious external machines
- Suspicious local machines
- Trusted IPs
- Trusted server sites
- Vendor and contractor accounts
- Vendor-authorized servers
The Admin Accounts group is used in several template rules as a placeholder for a custom list of administrative users. This group represents the default administrative accounts in Windows and Unix/Linux environments.
See the following topics for more information.
