Windows scripting in SAM component monitors
The Windows Script Monitor supports custom scripts on Windows-based systems. You can create multiple instances of this component monitor per template to run custom scripts.
This information details the format and usage of Windows Scripts for SAM, including script arguments and output formats. It does include details about coding in various programming languages.
Before coding and testing a script, review Create custom Windows scripts and Best practices for SAM templates. Sample script monitors are available on the SolarWinds Platform server at: C:\Program Files (x86)\SolarWinds\Orion\APM\SampleScriptMonitors
To display a list of out-of-the-box SAM templates that support Windows scripting:
- Navigate to the Manage Templates page.
- Click Settings > All Settings > SAM Settings > Manage Templates.
- On the Manage Application Monitor Templates page, enter Windows in the search field.
On Windows-based computers, you can use one of several scripting languages or install a non-native scripting language.
- Install the scripting language engine or software on the SolarWinds Platform server.
- Verify that the install location for the scripting language is in the system environment path variable.
-
In the SAM template, expand the details for the Windows Script Monitor and specify the scripting language in the Script Engine field.
How the Windows script works
The Windows Script Monitor executes the script on the SolarWinds Platform server connecting to the target server to collect metrics:
-
Executes the script using the script arguments on the SolarWinds Platform server.
- The monitor connects to the target server using entered credentials for collecting metrics.
- SAM parses the text output, saves data, and reports the values using the output formats from the component monitor.
Elements of a Windows script
SolarWinds recommends writing scripts in the Windows Script Monitor to verify correct access between the Main Polling Engine, SAM, and the target server(s). You can write and test scripts in your preferred Integrated Scripting Environment (ISE), connecting and testing against the target server to verify if the code functions. Test the script through the Windows Script Monitor to verify credentials and target server access, and to generate metrics output.
The script in the monitor should include:
- Parameters to run the script in the Scripts Arguments field
- Script code added in the Script Body field with credentials
- The script engine to use for the supported programming language
- Exit codes to report status in the script
- Formatted output after running the script
Test the component monitor and script before assigning and using the component monitor within a template as is. Testing the script generates the required database tables for metrics output and verifies output processes.
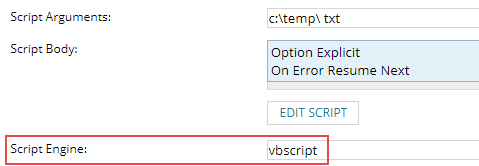
Script Arguments field
Use this field in the Edit Script window to specify arguments to pass to the script. You may include the variables ${IP} (or ${Node.DNS}), ${USER}, and ${PASSWORD}, which are replaced respectively by the IP address of the target node, the credential user name, and the credential password.
Script Body field
Use the Script Body field to enter your script code. You can write and compile the script in a language you prefer then copy and paste the code into this field. Depending on the language, you may need to take additional steps for the script and command line to execute.
Scripts must report their status by exiting with the appropriate exit code. The exit code is used to report the status of the monitor, displayed in the SolarWinds Platform Web Console. For details, see Report status through exit codes in SAM script monitors.
Specify the scripting language to be used. The default value is vbscript. Below is a list of scripting engines that the Windows Script Host supports:
Name File Extensions Availability VBScript
.vbs
Installed by default
JScript
.js
Installed by default
PerlScript
.pls
Freeware
ooRexxScript
.rxs
Freeware
PythonScript
.pys
Freeware
TclScript
.tcls
Freeware
ActivePHPScript
.phps
Freeware
RubyScript
.rbs
Freeware
Object Rexx engine
Commercial
Delphi scripting engine
Commercial
Note the following details:
- If the application monitor is set to Agentless, the VBScript runs on the Main Polling Engine (usually the SolarWinds Platform server).
- If the application monitor is set to Agent, the script runs on the target node.
- PowerShell uses WinRM that runs over TCP ports 5985 and 5986.
- All Linux, Unix, and Nagios script monitors use SSH over TCP Port 22.
Want to see how other SolarWinds customers use script monitors? Visit the Server & Application Monitor forum in THWACK.
