Configure Okta for single sign-on login to the SolarWinds Platform Web Console
This topic applies to all SolarWinds Platform products.
When configuring Okta to communicate with your SolarWinds Platform Web Console, you will be working with both Okta and SolarWinds Platform Web Console at the same time. You need to copy information from one system into the other.
Step 1: In the SolarWinds Platform Web Console, prepare the identity provider URL and URI
-
Log in to the SolarWinds Platform Web Console using an administrator account.
-
Click Settings > All Settings.
-
In the User Accounts section, click SAML Configuration.
-
Click Add Identity Provider.
-
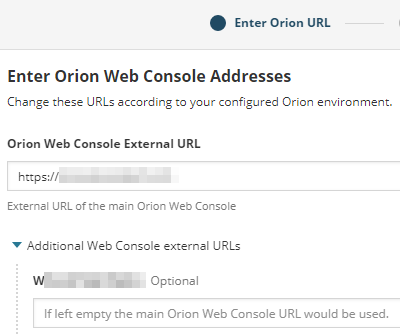
In the Enter Orion URL step, check that the external URLs are correct and adjust them if necessary.
SolarWinds Platform Web Console External URL
This is the URL of your SolarWinds Platform server or its DNS alias.
Additional Web Console external URLs
If you have additional polling engines deployed, check the URL(s) for the servers hosting the additional web console. The field should contain one of the following:
-
The address of the server hosting your Additional Web Console
Example:
https://WIN-1234567890A -
The DNS alias of the server hosting the Additional Web Console
Example:
https://orion -
No input
Clear the suggested URL. When you try to log in to the Additional Web Console using SAML authentication, you'll be redirected to the primary SolarWinds Platform Web Console
These URLs are used to generate the URL and URI you copy into your identity provider settings.
-
-
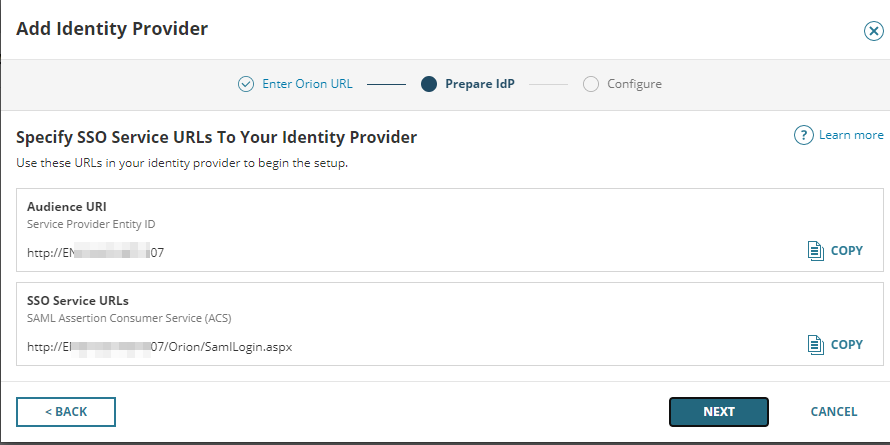
The Prepare IdP step provides Audience URI and SSO Service URL(s) to be copied and pasted into the configuration in Okta.
Keep the browser open, and continue in Okta.
If you have deployed additional web servers, the SSO Service URLs section includes more URLs - one for the primary SolarWinds Platform Web Console and one for each additional web server.
Step 2: In Okta, create the SAML application, configure URLs and the URI, and specify users for SAML login
If prompted to switch to the Classic UI, switch to the Classic UI.
-
Log in to your Okta organization with administrative privileges.
-
Click on the blue Admin button.
-
Click Add Applications > Create New App.
-
Select the SAML 2.0 option and click Next.
-
In General Settings, type the SAML Application Name in the App name field, and click Next.
-
In the SAML Settings section, make the following changes:
-
In the General section, paste the SAMLLoging URL of your SolarWinds Platform Web Console into the Single sign on URL.
Example:
https://hostname.domain/Orion/SAMLLogin.aspxThis is the SSO Service URLs to copy from the SolarWinds Platform Web Console. See Prepare the identity provider in the SolarWinds Platform Web Console.
-
If you have deployed an additional web server, configure the additional website:
-
Select the Allow this app to request other SSO URLs box.
-
In the Requestable SSO URLs, click Add Another, and provide the additional web server URL into the URL field. For example:
https://hostname.domain/Orion/SAMLLogin.aspxCopy the additional web console URL from SSO Service URLs in the SolarWinds Platform Web Console. See Configuring the identity provider in the SolarWinds Platform Web Console.
-
In the Index box, provide appropriate index value.
-
-
Enter the address of your SolarWinds Platform Web Console to Audience URI (SP Entity ID)
Example:
http://hostnameThis is the Audience URI to copy from the SolarWinds Platform Web Console. See Prepare the identity provider in the SolarWinds Platform Web Console.
-
In the Attribute Statements section, add following attribute statements:
Name Name format Value Email Unspecified user.email FirstName Unspecified user.firstName LastName Unspecified user.lastName -
Add following to the Group Attributes Statements:
Name Name format Filter Value OrionGroups Unspecified Matches regex .* - Click Next, provide the requested background information about you, and click Finish.
-
- Specify users to access the SolarWinds Platform Web Console through SAML login:
- In Okta, click Assignments > Assign, and select Assign to People.
- Select users and click Assign.
- When you assign SAML login for the SolarWinds Platform Web Console to all required users, click Done.
- On the Sign On tab, click the View Setup Instructions button in the Sign On Methods section. Keep the tab open, so that you can copy and paste the details into the SolarWinds Platform Web Console.
Step 3: Complete the identity provider configuration in the SolarWinds Platform Web Console
-
Switch to the SolarWinds Platform Web Console. You have the Add Identity Provider wizard open on the Prepare IdP step. Click Next.
-
Identity Provider Name: specify how the identity provider will be displayed on the login page. Use for example 'Okta'.
-
SSO Target URL
Example:
https://www.okta.com/app/app_name_example_1/xyz/sso/saml -
Issuer (Entity ID)
Example:
http://www.okta.com/abcdefgh123456ijkl789 -
Public Certificate - Certificate in Base64 form
Copy the contents of the certificate, starting with BEGIN CERTIFICATE and ending with the END CERTIFICATE line.
-
Save the configuration.
In the Configure step, paste the information from the Okta tab with configuration details you left open.
When logging to the SolarWinds Platform Web Console, users now see an additional button Log In with Okta. To enable users to log in using single sign-on, create SAML users or SAML user groups for the users.
Step 4: Define users for SAML login using Okta in the SolarWinds Platform Web Console
-
In the SolarWinds Platform Web Console, click Settings > All Settings, and then click Manage Accounts in the User Accounts section.
-
Click Add New Account.
-
Define the SAML individual user or group.
Create SAML individual user account
- Select SAML individual account.
- Provide Name ID. Use the same user name the user has in Okta. You have already assigned SAML login to the user.
- Specify what the user can access and do, and then complete the wizard.
Create SAML group account
- Select SAML group account.
-
Provide the name for the group. Use the group name you assigned SAML login to in Okta.
The SAML Group and the Identity Provider Group Name must match.
- Specify what users in the group can access and do, and complete the wizard.
Users now can log in to the SolarWinds Platform Web Console by clicking the Login with Okta button on the login page and providing their Okta credentials.
Disclaimer: Please note, any content posted herein is provided as a suggestion or recommendation to you for your internal use. This is not part of the SolarWinds software or documentation that you purchased from SolarWinds, and the information set forth herein may come from third parties. Your organization should internally review and assess to what extent, if any, such custom scripts or recommendations will be incorporated into your environment. You elect to use third-party content at your own risk, and you will be solely responsible for the incorporation of the same, if any.
