Send Your Logs to Loggly
Navigation Notice: When the APM Integrated Experience is enabled, Loggly shares a common navigation and enhanced feature set with other integrated experience products. How you navigate Loggly and access its features may vary from these instructions.
Loggly supports any text-based log data. The most common way to send system and application logs to Loggly is using a local syslog agent. Below are the instructions to send system and application logs using a local syslog agent in either a Linux or Windows environment. For other methods of sending log data to Loggly, see Logging Setup.
Sending Logs from a Linux Syslog Agent
The following script run in just a few seconds and will perform several system compatibility checks, configure rsyslog using best practices, and verify the logs reach to our system. It assumes you have sudo access, you’re on a common linux distribution with rsyslog 5.8 or higher, it receives local system logs, and port 514 (insecure logging port) 6514 (secure logging port) is open to outbound connections.
Configure-linux script
This script sends the system logs to Loggly. The script by default send the logs securely but if package manager (rsyslog-gnutls) could not be installed in your distribution then it will ask to switch to the insecure mode in order to send logs successfully. Run the automatic configure-linux bash script below to setup rsyslog. Alternatively, you can manually configure rsyslog.
curl -O https://www.loggly.com/install/configure-linux.sh sudo bash configure-linux.sh -a <subdomain> -t <token>-u <username>
Replace:
- <subdomain>: your account subdomain that you created when you signed up for Loggly
- <token> (optional): your customer token from the source setup page
- <username>: your Loggly username
Script Usage
configure-linux [-a loggly auth account or subdomain] [-t loggly token (optional)] [-u username] [-p password (optional)] [-s suppress prompts (optional)] [--insecure {Insecure mode} (optional)] [--force-secure {Force Secure Mode} (optional)]
Configure
- Configures rsyslog to send logs to Loggly
Suppress prompts
- Suppressing the interactive prompts allows you to run it automatically using default settings
Insecure Mode
- Insecure mode allows you to send your logs insecurely on port 514
Force Secure Mode
- Force secure will send the logs forcefully to secure mode. It prevents swiching to insecure mode even if package rsyslog-gnutls could not be downloaded. This will set the TLS configurations. On manually installing the rsyslog-gnutls package, secure sending will be started.
The script will perform over 10 system checks below to make sure your system is compatible with Loggly and that it can successfully send logs to Loggly. It also logs the status of your setup experience to Loggly so our support team can help if you have trouble.
Sending Logs from a Windows Syslog Agent
Make sure to replace the CUSTOMER_TOKEN in the config file with your specific token found under Source Setup > Customer Tokens.
1. Install Nxlog
Download the latest version of nxlog. It’s probably easiest to choose the Windows msi file which includes an installer.
2. Copy the Configuration
Open the Nxlog configuration file at:
C:\Program Files (x86)\nxlog\conf\nxlog.conf
Replace the entire configuration file by pasting the following, and replacing the variables below.
## This is a sample NXLog configuration file created by Loggly. June 2013 ## See the nxlog reference manual about the configuration options. ## It should be installed locally and is also available ## online at https://nxlog.org/nxlog-docs/en/nxlog-reference-manual.html ## Please set the ROOT to the folder your nxlog was installed into, ## otherwise it will not start. #define ROOT C:\\Program Files\\nxlog #define ROOT_STRING C:\\Program Files\\nxlog define ROOT C:\\Program Files (x86)\\nxlog define ROOT_STRING C:\\Program Files (x86)\\nxlog define CERTDIR %ROOT%\\cert Moduledir %ROOT%\\modules CacheDir %ROOT%\\data Pidfile %ROOT%\\data\\nxlog.pid SpoolDir %ROOT%\\data LogFile %ROOT%\\data\\nxlog.log # Include fileop while debugging, also enable in the output module below #<Extension fileop> # Module xm_fileop #</Extension> <Extension json> Module xm_json </Extension> <Extension syslog> Module xm_syslog </Extension> <Input internal> Module im_internal Exec $Message = to_json(); </Input> # Windows Event Log <Input eventlog> # Uncomment im_msvistalog for Windows Vista/2008 and later Module im_msvistalog #Uncomment im_mseventlog for Windows XP/2000/2003 #Module im_mseventlog Exec $Message = to_json(); </Input> <Processor buffer> Module pm_buffer # 100Mb disk buffer MaxSize 102400 Type disk </Processor> <Output out> Module om_tcp Host logs-01.loggly.com Port 514 Exec to_syslog_ietf(); Exec $raw_event = replace($raw_event, 'NXLOG@14506', 'TOKEN@41058 tag="windows"] [', 1); </Output> <Route 1> Path internal, eventlog => buffer => out </Route>
Replace the above variables:
- CUSTOMER_TOKEN: Replace with your own customer token
- ROOT and ROOT_STRING: If you are in 32-bit Windows, uncomment the top root path on lines 8 and 9 to use the 32-bit program files folder then comment the two below.
Note: The pm_buffer module supports disk based message buffering and helps in storing logs during network outage, it also send buffered logs when network connection is re-established. You can increase or decrease the MaxSize under the pm_buffer module according to your requirement of disk buffer.
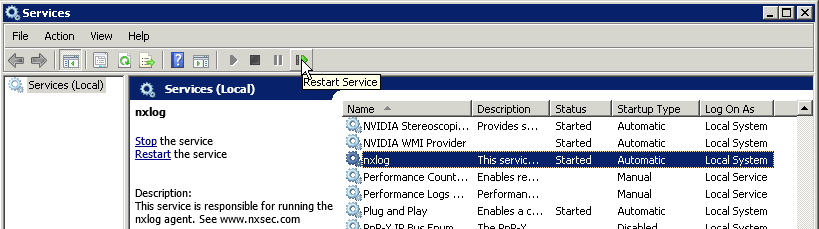
3. Restart Nxlog
Open the Services tool in the Start menu, find nxlog in the list, and then restart the service.
Next Steps
Once you've configured your syslog agent, Loggly, View Your Loggly Data to ensure it was sent correctly.
The scripts are not supported under any SolarWinds support program or service. The scripts are provided AS IS without warranty of any kind. SolarWinds further disclaims all warranties including, without limitation, any implied warranties of merchantability or of fitness for a particular purpose. The risk arising out of the use or performance of the scripts and documentation stays with you. In no event shall SolarWinds or anyone else involved in the creation, production, or delivery of the scripts be liable for any damages whatsoever (including, without limitation, damages for loss of business profits, business interruption, loss of business information, or other pecuniary loss) arising out of the use of or inability to use the scripts or documentation.
