File Watching monitor
The File Watching monitor reads file content one line at a time, making it ideal for locating various types of information recorded in application or server log files, such as errors, events, and notices. Syslog files, which are sent across the network to a syslog server rather than being recorded locally, can also easily be monitored using the File Watching Monitor.
The monitor scans your selected file and locates any entries that match your defined regular expressions. Regular expression searching is ideal for filtering specific details from the lines in a file because the format and contents in log files may vary significantly depending on the recorded information. When a match is found, a content generator that you configure parses the information and generates an Information alert.
You can configure the monitor to only trigger a single Information alert per scan, as opposed to one per match. This can significantly reduce the number of alerts you receive. The monitor maintains a pointer to the file offset, ensuring that lines are only analyzed once. If the log file is reset, the pointer is reset as well.
After you create a new File Watching monitor, the monitor begins searching forward from that point in time. It does not search historical content included in the file.
Other monitor types may include Force Test to reset the monitor testing cycle so you can reapply new configuration parameters. This process does not work with the File Watching monitor because its pointer will be reset to its current time—basically, the end of the file.
Create a File Watching monitor
- Click Devices in the toolbar.
- Locate and click the targeted device you want to monitor.
-
In the toolbar, click Add > Add New Monitor.
- In the Select Monitor menu, click File Watching.
-
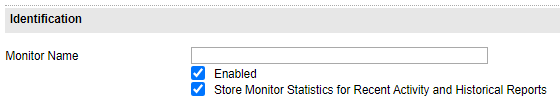
Complete the fields in the Identification section.
-
Under Identification, enter a monitor name using up to 64 characters.
This name will appear in the Monitors List, Monitor Status, Logs pages, and your reports.
You can change this name later, if necessary. ipMonitor does not use this field to internally identify this monitor.
-
Select Enabled to enable the monitor.
When enabled, the monitor tests the specified resource using the settings you enter under Test Parameters. You can disable the monitor later if required.
- (Optional) Select Store Monitor Statistics for Recent Activity and Historical Reports to enable this functionality.
-
-
Complete the fields in the Test Parameters section.
See Test Parameters example for an example of how to complete this section.
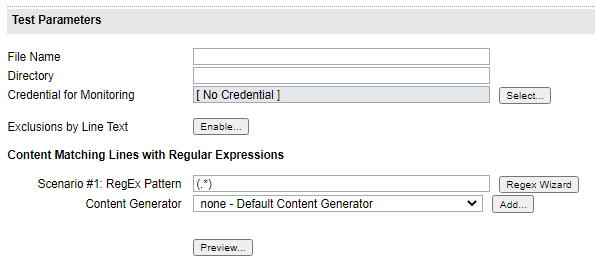
- In the File Name field, enter the name of the file you want to monitor.
-
In the Directory field, enter the Local or UNC path to the file.
An example UNC path would be
\\ServerName\ShareName.An example of a local path would be
C:\\Windows\. -
Select a credential for monitoring. When selected, ipMonitor uses the credential account and password information to authenticate to the target machine and test the status of the drive or share.
- If you are creating a regular expression using the RegEx Wizard, click Exclude to exclude the file content based on the expression.
- Under Content Matching Lines with Regular Expressions, enter a regular expression to compare against the event description string.
- Click the Content Generator drop-down menu and select the content generator used to extract the specific data from the Event Log contents.
- Click Preview to search the file's existing content. This can be helpful for configuration and troubleshooting purposes.
-
Under Timing, configure the fields for the monitor testing states.
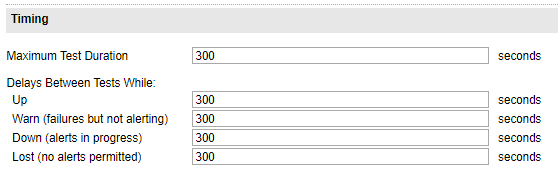
- In the Maximum Test Duration field, enter the maximum test duration rate (in seconds) that the monitor times out before the test is considered a failure.
-
In the remaining fields, enter the number of second between each test while the monitor is in an OK state (Up), a failed state while alerts are processed (Down), and a failed state and the maximum number of alerts have been processed (Lost).
In the Lost state, no additional failure alerts are processed. However, a recovery notification is sent if the monitor recovers.
-
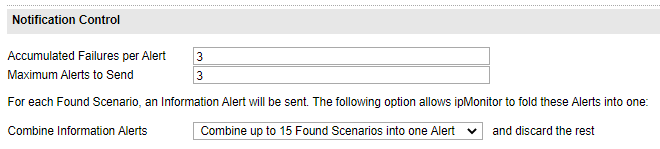
Under Notification Control, complete the fields to determine how many test failures must occur before an alert is sent.
-
Enter the number of test failures that occur for each alert before ipMonitor generates an alert for the monitor.
Each time a monitor test fails during a Warn state, a sequential failure count incremented against this value. A successful test resets the accumulated failure count to zero.
The default option is 3.
-
Enter the maximum number of alerts to send before the monitor enters a Lost state.
A successful test while in the Down or Lost state resets the alert sequence.
- Click the Combine Information Alerts drop-down menu and select whether to combine multiple failures in a single test to a single alert or disable this function.
-
-
Under Recovery Parameters, complete the fields to indicate the corrective action used to automatically restore a resource using the External Process Recovery, Reboot Server Recovery, or Restart Service Recovery action.
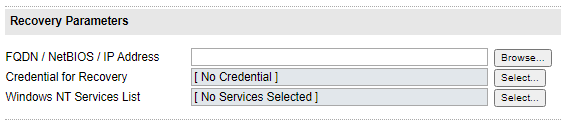
- Enter the Fully Qualified Domain Name (FQDN), NetBIOS, or IP Address of the machine hosting the service that needs a restart or the machine that needs a restart. You can also click Browse to locate and select the machine.
- Select the set of credentials used by the recovery alert. You can select a specific credential to execute recovery alerts that require access to restricted resources, such as Reboot Server, Restart Service, or External Process.
- Select the list of services to restart on the target machine specified in the FQDN/NetBIOS/IP Address field. This field is only required for the Restart Service alert. If a service has dependencies, select all dependent services.
- Click OK.
Test Parameters example
Most servers and server applications are capable of recording system errors to a log file. You can use ipMonitor to search through the contents of a log file for specific entries based on user-defined criteria, or a regular expression. When a match is found, this information can be extracted from the file and formatted using a content generator before it is sent to an Information alert.
Below is a sample line for a Syslog:Cisco PIX firewall:
Jul 29 2004 09:56:27: %PIX-1-103003: (Primary) Other firewall network interface 4 failed.
Monitor configuration settings
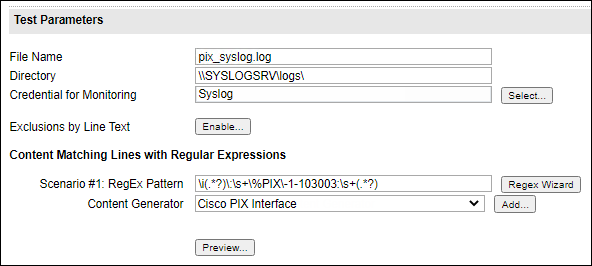
File Name: pix_syslog.log
Directory: \\SYSLOGSRV\logs\
Scenario #1: RegEx Pattern \i(.*?)\:\s+\%PIX\-1-103003:\s+(.*?)
Content generator
After you apply the configuration settings, create a content generator to insert the results into an email message body or other action type when an action is triggered.
A content generator is created in the Alerts or Content Generators section, as shown below.
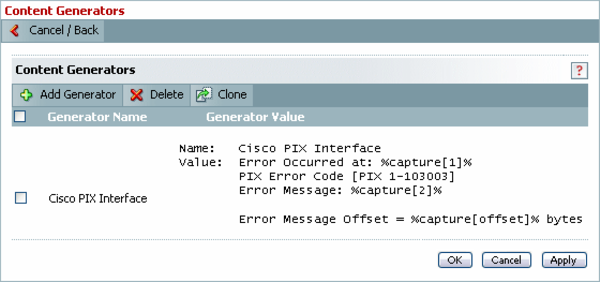
Name: Cisco PIX Interface
Value: Error Occurred at: %capture[1]% PIX Error Code [PIX 1-103003] Error Message: %capture[2]%
Error Message Offset = %capture[offset]% bytes
After the content generator is created and saved, assign the new content generator to the File Watching monitor in the Information alert content menu, located in the Monitor configuration page.
Information alert results
The following is a sample of the formatted result when ipMonitor finds an entry in the file matching the regular expression.
Error Occurred at: Jul 29 2019 09:56:27 PIX Error Code [PIX-1-103003] Error Message: (Primary) Other firewall network interface 4 failed.
Error Message Offset = 23698 bytes
